A new report from the U.S. Government Accountability Office (GAO) released Tuesday found “mission-critical cyber vulnerabilities” while testing new Department of Defense (DoD) weapons systems. The GAO also noted that program officials the agency met with “believed their systems were secure and discounted some test results as unrealistic.”
Given that the Pentagon is spending some $1.66 trillion on developing new, sophisticated weapons, the GAO notes that “it is important that [the systems] work when needed, yet cyber attacks have the potential to prevent them from doing so.”
This is not an entirely new issue. In a 1996 report on cybersecurity, the GAO noted that the DoD may have been the target of as many as 250,000 cyberattacks in 1995 and declared, “The potential for catastrophic damage is great.”
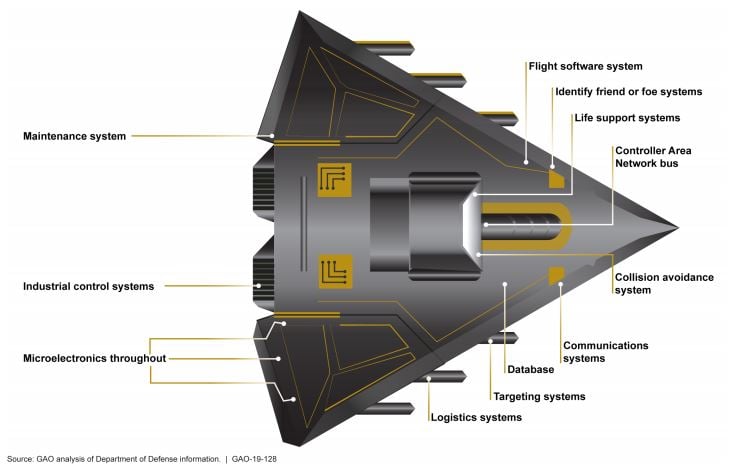
The problem has only gotten worse because “nearly every conceivable component in DoD is networked.” Pentagon weapons systems are more connected than ever and that can lead to the introduction of vulnerabilities that make the systems more difficult to defend.
[nativounit]
According to the new report, the Director of Operational Test and Evaluation noted that prior to around 2014, program offices actually tried to avoid cybersecurity assessments because the programs had no cybersecurity requirements and, for that reason, should not be evaluated. The GAO commented:
Due to this lack of focus on weapon systems cybersecurity, DOD likely has an entire generation of systems that were designed and built without adequately considering cybersecurity. Bolting on cybersecurity late in the development cycle or after a system has been deployed is more difficult and costly than designing it in from the beginning. Not only is the security of those systems and their missions at risk, the older systems may put newer systems in jeopardy.
The situation has not improved much since 2014:
[GAO] found that from 2012 to 2017, DOD testers routinely found mission-critical cyber vulnerabilities in nearly all weapon systems that were under development. Using relatively simple tools and techniques, testers were able to take control of these systems and largely operate undetected. In some cases, system operators were unable to effectively respond to the hacks. Furthermore, DOD does not know the full scale of its weapon system vulnerabilities because, for a number of reasons, tests were limited in scope and sophistication.
Testing teams were able easily to gain access to and take control of some weapons systems using only basic tools including just guessing the administrator password or looking it up because the password had never been changed from the default. Even when program offices were aware of vulnerabilities that had been identified in the past, those vulnerabilities had not been resolved. GAO noted that one test report showed that only one of 20 cyber vulnerabilities discovered in a previous test had been corrected.
The GAO did not make any recommendations in its new report and said that it would continue to evaluate the issue. The agency did note that the DoD had taken several recent steps to improve the cybersecurity of weapons systems, but that it faces barriers that could limit the effectiveness of those steps, citing specifically the challenges of hiring knowledgeable staff and difficulties in sharing information and lessons-learned across service boundaries.
The full report, along with additional highlights and other material, is available at the GAO website.
[recirclink id=497788]
[wallst_email_signup]














